Managed Security Services
Orange County, Irvine, Santa Ana, Los Angeles
Managed Security Services & Security Assessment
Is Your Network Secure From Hackers and Cyber Attackers?
Managed Security Services Help You to Conduct IT Security Audit Before Regulatory Compliance Audit
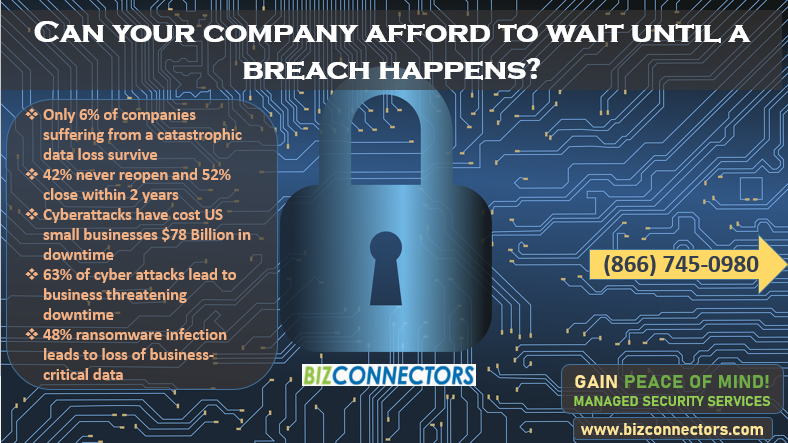
No One Needs to Convince You Cybersecurity is Vital to Your Business
Did You Know That Ransomware Has Exploded Whopping 390% Between 2020-2022?
Ransomware Damages Cost 137$ Billion in 2019 and $176 Billion in 2020!
Average Cost To Recover From Ransomware Skyrocketed in 2020
Managed Security Services & Cyber Security Services Can Help
As the threat landscape becomes increasingly sophisticated, it’s clear that a layered approach to cybersecurity is key to delivering superior results. By deploying layer security that extends endpoint protection into the network, we can ensure that most internet threats are blocked before they even reach our clients’ endpoints. With Managed Security Services deploying protection at the network edge and endpoint protection for network-connected devices, we can provide powerful, comprehensive security to our clients that is easy to manage and cost-effective.
What are the most known causes of ransomware infections?
- Phishing emails
- Lack of employee cybersecurity training
How serious is the threat of ransomware for small and medium businesses?
- Cybercrime is expected to cost companies $6 trillion worldwide by 2021
- Ransomware has cost US small businesses $75 Billion in downtime
- 63% ransomware attack leads to business threatening downtime
- 48% ransomware infection leads to loss of business-critical data
FBI reports show that ransomware was the most pervasive threat of 2016. On average, 4,000 ransomware attacks occurred every day in 2016, and costs might add up to $60 billion. This trend continued all through 2017 and with ransomware being so profitable, there is no doubt it will continue to be a threat in 2018.
FREE 30 Minutes Consultation!
Identify Your Network Vulnerabilities Now! Its Free And Confidential
TOTAL RANSOM PAID BY SMBs TO RANSOMWARE HACKERS IN Q2 of 2017 and 2018 WAS $421 MILLION!
Information systems are constantly affected by security incidents, such as human mistakes, natural events, technical failures or malicious attacks. These incidents are becoming bigger, more frequent, and more complex. As such, network and information security management are increasingly important to any business operations.
Lack of network and information security can compromise the vital services depending on the integrity of network and information systems. Consequently, it could stop the business from functioning and could generate substantial financial losses for the company.
The resilience and stability of network and information systems are therefore essential to the completion of the company’s smooth functioning of data processing and business processes as a whole.
Government contracting places additional protection and security obligations on government suppliers and vendor’s capability that should ensure the security of DoD shared information and specific incident reporting requirements.
A step-change is therefore needed in the way network and information security are designed, implemented, monitored and reported.
What is the best solution?
We believe that organizations need to start with the basic IT Security measures followed by building up the multi layer security measures (systems, policies, behaviors). Next, perform regular pro-active network security audits to confirm that those security measures have addressed all of the external and internal vulnerabilities.
According to the US Department of Homeland Security #1 solution for ransomware protection are backup and disaster recovery solution!
A well-maintained business continuity and disaster recovery solution can drastically lower the risk and costs of ransomware by limiting downtime.
What is Managed Security Services and how can it benefit my business?
Bizconnectors Security Services through on-going security monitoring and assessment exposes threats and vulnerability and keeps your systems in check! With our security monitoring, network tools and reporting service, we can ensure that most internet threats are blocked before they even reach your endpoints. We will also keep an eye on a wide array of security reports and alerts such as:
- Anomalous Login
- External Vulnerability Scan Detail
- External Vulnerability Scan Detail by Issue
- External Vulnerability Summary
- Outbound Security
- Security Policy Assessment
- Share Permission Report by Computer
- Share Permission Report by User
- User Behavior Analysis
- Login History by Computer
- Login Failures by Computer
- Data Breach Liability
We dive deep into the policies, systems, and behavior to identify aspects of security that need immediate change or corrections. Once we identify any risk, we will immediately start working on solutions that address these issues to provide a more secure environment for your whole organization.
Enjoy business continuity, efficiency, and resiliency!
Today businesses are operating in the Internet environment with over 500,000 malware floating around the net per day! Over the last 4 years, threats have been accelerating at a compounding rate and every day more sophisticated attacks such as polymorphic malware, malware injected in paid advertising and ransomware are designed and deployed by hackers throughout the Internet.
Therefore, cybersecurity, network, and information technology security are becoming extremely vital and essential for any business today.
Find out how to protect your business against ransomware attacks now!
Call 866-745-0980 for a Free Consultation
Proactive Remote Monitoring: provides remote monitoring of your systems and networking that triggers alerts to be sent to designated people to inform them about the found vulnerability.
Contact a Bizconnectors Managed Security Service Representative at (866) 745-0980
Identify Your Network Vulnerabilities Now! Its Free And Confidential
How May We Help You?
Simply fill out the form on this page and one of our consultants will promptly call you for your free consultation!
Here is the step by step how to get started:
- Fill out the form on this page or simply call us.
- We will have a conversation that will lead to understanding your needs and concerns.
- Allow us to create a customized plan.
- Let’s execute the plan together.
100% Free & No-Risk. You are never obligated to pay us or work with us just to have a free consultation with our consultants!
Want to call us instead? Call us at 866-745-0980 right now!
Do You Need Consultation Before Making a Decision?
We are here to help you with any questions you have and provide you with more information about how Managed Security Services & Cyber Security Services can increase the safety of your business.
Call (866) 745-0980 or fill out and submit the form on this page to get answers to all your questions now!
100% Satisfaction Guaranteed or Your Money Back!

You’re ”Thrilled Today Or You Don’t Pay” 100% Money Back Guarantee!
